What is a security strategy?
 Ava Wright
Ava Wright 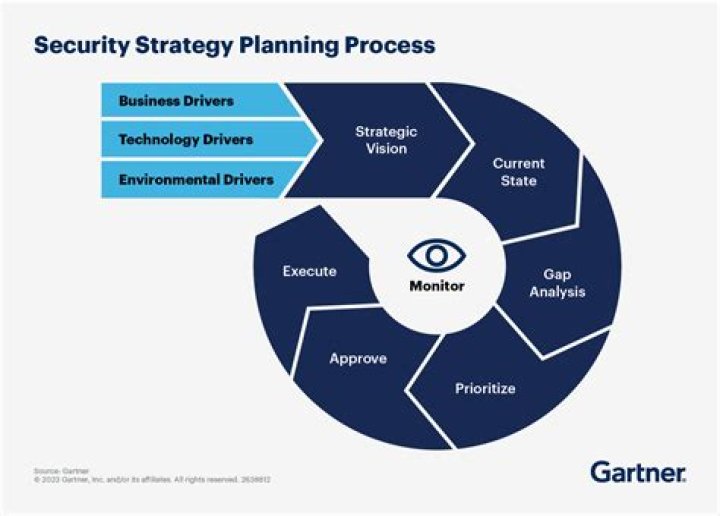
Keeping this in view, how do you write a security strategy?
Consider a written security policy as one of your controls to mitigate risk to your data assets.
- Below is an example of a potential written security policy framework.
- Organize your framework so that it is easy to navigate.
- List your physical assets.
- List the risks to your physical assets.
Beside above, what is a cyber security strategy? A national cybersecurity strategy (NCSS) is a plan of actions designed to improve the security and resilience of national infrastructures and services. It is a high-level top-down approach to cybersecurity that establishes a range of national objectives and priorities that should be achieved in a specific timeframe.
Also to know is, what is the primary objective of a security strategy?
Ensure compliance with security policy and standards by establishing appropriate procedures, access and requirements for end users. Protect the confidentiality, integrity and availability of the organization's information and information assets.
How do you create a cyber security strategy?
7 Steps to Building a Cybersecurity Strategy from Scratch
- Start by identifying your greatest business needs.
- Conduct a third-party security assessment to identify and remediate the greatest vulnerabilities to your business needs.
- Engage a Network Specialist to set-up a secure network or review your existing network.
Related Question Answers
What are the four objectives of planning for security?
modify the security program to existing or new environments; align services and support with business objectives; validate and measure our results and value; identify risks, get management input, and develop priorities and consensus on risk mitigation; and.How can a business improve its security?
6 Simple Tips to Increase Your Small Business Security Using Inexpensive Cybersecurity Measures- Change Your Passwords.
- Use a Password Manager.
- Delete Any Unused Accounts.
- Enable Two-Factor Authentication.
- Keep Your Software Up to Date.
- Training to Identify Phishing and Spear Phishing Attacks.
What are the aims of security?
The Four Objectives of Security: Confidentiality, Integrity, Availability, and Nonrepudiation. Roles and Responsibilities. Security Policy.What are the objectives of security education?
Security Awareness Goals and Objectives The primary objective of a security awareness program is to educate users on their responsibility to help protect the confidentiality, availability and integrity of their organization's information and information assets.What are the two primary objectives of security controls?
The Primary Objectives of Data Security Data security controls that promote least privilege include ACLs, encryption, two-factor authentication, strict password protocols, configuration management, and security monitoring and alerting software.What is an example of a physical security measure?
This includes protection from fire, flood, natural disasters, burglary, theft, vandalism and terrorism. Such hardening measures include fencing, locks, access control cards, biometric access control systems and fire suppression systems.What is an information security strategy?
An information security and risk management (ISRM) strategy provides an organization with a road map for information and information infrastructure protection with goals and objectives that ensure capabilities provided are aligned to business goals and the organization's risk profile.What are the information security objectives?
Computer security has four objectives: confidentiality, integrity, availability, and nonrepudiation (NR). Securing information is equivalent to ensuring that computers keep your secrets, hold valid information, are ready to work when you are, and keep records of your transactions. Figure 1–1 shows the four objectives.Why do we need security awareness training?
Security awareness training is all about teaching your colleagues and employees to understand the risks and threats around the ever evolving cyber world. Security awareness training also ensures that employees are fully awake to the consequences of failing to protect the organisation from outside attackers.What is information security and control state its objectives?
The overall objective of an information security program is to protect the information and systems that support the operations and assets of the agency. – Availability - Defending information systems and resources to ensure timely and reliable access and use of information.What kind of attack would a flood guard protect a network from?
flood guards serve as preventive control against denial-of-service (DoS) or distributed denial-of-service (DDoS) attacks. Flood guards are available either as standalone devices or as firewall components. It is capable of monitoring network traffic to identify DoS attacks in progress generated through packet flooding.What are the 4 types of cyber attacks?
Common types of cyber attacks- Malware. Malware is a term used to describe malicious software, including spyware, ransomware, viruses, and worms.
- Phishing.
- Man-in-the-middle attack.
- Denial-of-service attack.
- SQL injection.
- Zero-day exploit.
- DNS Tunneling.
What are the three types of security?
Principle 8: The Three Types of Security Controls Are Preventative, Detective, and Responsive. Controls (such as documented processes) and countermeasures (such as firewalls) must be implemented as one or more of these previous types, or the controls are not there for the purposes of security.What are the 10 Steps to Cyber Security?
What are the 10 steps to cyber security?- Risk management regime.
- Secure configuration.
- Home and mobile working.
- Incident management.
- Malware prevention.
- Managing user privileges.
- Monitoring.
- Network security.