What is a PGP key server and why would you need to use it?
 Michael Henderson
Michael Henderson 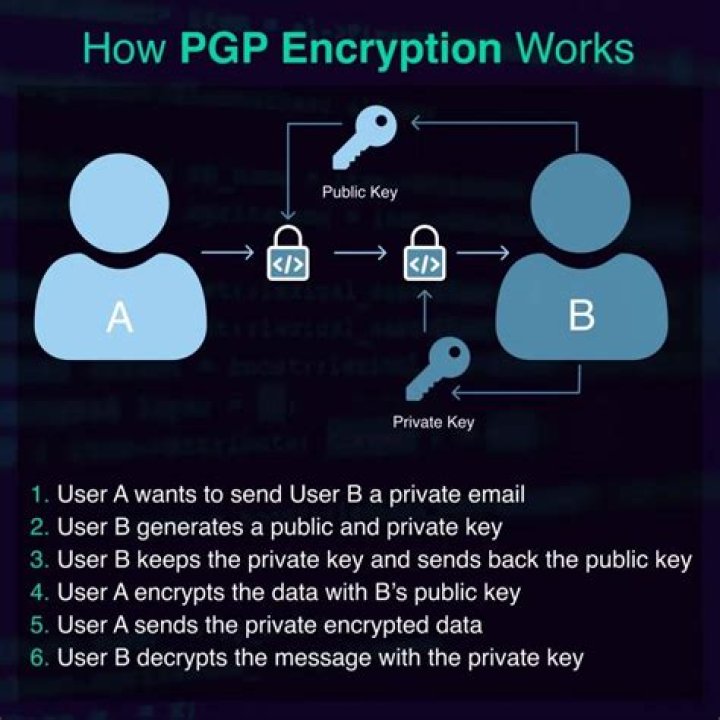
Similarly, you may ask, what is a PGP key used for?
Pretty Good Privacy (PGP) is an encryption system used for both sending encrypted emails and encrypting sensitive files. Since its invention back in 1991, PGP has become the de facto standard for email security.
One may also ask, where do I get PGP key?
- Download Gpg4win.
- Install Gpg4win.
- Once everything is installed, find the Kleopatra program on your computer and open it.
- Go to the “File” tab and select “New Certificate.”
- Since you want PGP keys, select “Create a personal OpenPGP key pair.”
Keeping this in view, what are the five principles services provided by PGP?
S/MIME is discussed in detail in the recommended text.
- 12.1 Background. PGP is a remarkable phenomenon.
- 12.2 Operational Description.
- 12.2.1 Authentication.
- 12.2.2 Confidentiality.
- 12.2.3 Confidentiality and Authentication.
- 12.2.4 Compression.
- 12.2.5 E-mail compatibility.
- 12.2.6 Segmentation.
How do I setup a PGP key?
Create a Keypair
- Open Encryption Desktop.
- Select the PGP Keys Control box.
- Click the File > New > PGP Key.
- When the Key Generation Assistant appears, click Next.
- Enter a Full Name and Primary Email address for the key.
Related Question Answers
Does Gmail use PGP?
Gmail encryption: End-to-end encryptionFlowCrypt adds a special "Encrypt and Send" button into your inbox interface, which allows you to send encrypted messages using the PGP (Pretty Good Privacy — yes, that's actually what it's called) standard.
How does PGP use the concept of trust?
PGP uses a Web of trust model to authenticate digital certificates, instead of relying on a central certificate authority (CA). If you trust that my digital certificate authenticates my identity, the Web of trust means you trust all the digital certificates that I trust.Which algorithm can be used to sign a message?
Which algorithm can be used to sign a message? Explanation: Public key algorithms are used to sign a message and private key algorithms are used to encrypt the messages. Explanation: Some examples of hash functions are MD5 and SHA-1.How do I read a PGP message?
Decrypt an encrypted file- Double click the file to be decrypted.
- You may also right click the file to be decrypted, point to PGP, then click Decrypt & Verify.
- Enter the passphrase for your private key (or if the file was conventionally encrypted, enter the passphrase chosen by the file's encrypting user).
- Click OK.
How long is a PGP key?
A PGP key ID is just the bottom 64 bits of the public modulus (but only the bottom 32 bits are displayed with pgp -kv). It is easy to select two primes which when multiplied together have a specific set of low-order bits. This makes it possible to create a fake key with the same key ID as an existing one.What is PGP and how it works?
When a user encrypts plaintext with PGP, PGP first compresses the plaintext. This session key works with a very secure, fast conventional encryption algorithm to encrypt the plaintext; the result is ciphertext. Once the data is encrypted, the session key is then encrypted to the recipient's public key.What is a PGP public key?
PGP, Pretty Good Privacy, is a "public key cryptosystem." (Also known as PKC.) You use public keys to encrypt messages and files for others or to add users to PGP Virtual Disk volumes. You use your private key to decrypt files and messages that are encrypted with your public key.How does email PGP work?
PGP is a cryptographic method that lets people communicate privately online. When you send a message using PGP, the message is converted into unreadable ciphertext on your device before it passes over the Internet. Only the recipient has the key to convert the text back into the readable message on their device.What are the various PGP services?
PGP offers five basic services. Two of those are authentication and confidentiality; these can be combined.How does PGP provide authentication?
PGP provides authentication through the use of Digital Signature. It provides confidentiality through the use of symmetric block encryption. It provides compression by using the ZIP algorithm, and EMAIL compatibility using the radix-64 encoding scheme.What are the requirements for message authentication?
Message Authentication Requirements- Disclosure: Release of message contents to any person or process not possess- ing the appropriate cryptographic key.
- Traffic analysis: Discovery of the pattern of traffic between parties.
- Masquerade: Insertion of messages into the network from a fraudulent source.
Which algorithm is used for public key encryption?
RSA public key algorithmWhat is the difference between confidentiality and authenticity?
Confidentiality: Confidentiality is used to make sure that nobody in between site A and B is able to read what data or information is sent between the to sites. Authenticity: And this last sentence of the confidentiality part leads directly to the authenticity part.Does hashing provide confidentiality?
What is Hashing? Whereas encryption algorithms are reversible (with the key) and built to provide confidentiality (some newer ones also providing authenticity), hashing algorithms are irreversible and built to provide integrity in order to certify that a particular piece of data has not been modified.What is the need of key ID in PGP?
PGP uses key IDs to refer to public keys for a variety of purposes. These are not, properly speaking, fingerprints, since their short length prevents them from being able to securely authenticate a public key. 32bit key ids should not be used as current hardware can generate 32bit key id in just 4 seconds.Which should be used first to decrypt?
Explanation: The recipient should first decrypt the message using private key and then with the public key. Explanation: The digital signature provides authentication to both the sender and the message.How do I get my Android PGP key?
To use OpenPGP encryption with support for PGP/MIME on an Android device, you will require additional apps from the Google Play Store.To do so, proceed as follows:
- Open the email.
- In the email, tap show attachments.
- Tap open. Squeaky Mail automatically recognises the key and opens PGP KeyRing, to import the key.
What is the best PGP software?
Here are some of the top offerings.- OpenPGP. You may have heard about PGP (Pretty Good Privacy) software.
- GNU Privacy Guard. GNU Privacy Guard (GnuPG) is a popular software for email encryption and is an implementation of PGP.
- Gpg4win.
- Mailvelope.
- Enigmail.
- eM Client.
- Tutanota.
- CipherMail.
How do I share a PGP public key?
Share your public keys- Select GnuPG keys from the left side panel.
- From the list, select the Personal PGP key you want to publish.
- Select Remote ? Sync and Publish Keys….
- Press the Key Servers button to see the list of key servers on which you can publish your public key.
How do I open PGP encrypted files?
If it was encrypted using a key, the passphrase will be that of the recipient key.pgp) and enter the passphrase, or do the following:
- Open PGP Desktop.
- Locate PGP Zip Control box in the left pane of the PGP Desktop main screen.
- Click Open a PGP Zip.
- Browse to the PGP Zip file (e.g. filename. pgp), and click Open.
How do I send a PGP message?
Sending a digitally signed and / or encrypted email- Compose the message as usual.
- To digitally sign a message, select OpenPGP from the Thunderbird menu and enable the Sign Message option.
- If your email address is associated with a PGP key, the message will be encrypted with that key.
- Send the message as usual.
How do I encrypt a message with a public key?
- Install GPG. First, GPG must be installed.
- Generate your public and private keys. The first thing we'll do is generate a pair of keys.
- Export your public key.
- Exchange public keys with Alice.
- Import Alice's public key.
- Review the keys in your keyring.
- Encrypt the message you want to send.
- Decrypt message you've received.